Recently we see more and more customers and prospects being targeted for cryptomining attacks. This is increasing significantly as organizations transition to the cloud, and VM-based architectures continue to dominate compute-centric workloads. To enhance the security of these deployments, we are excited to introduce a threat detection feature in Security Command Center (SCC): Virtual Machine Threat Detection (VMTD). VMTD is a pioneering detection capability offered by a major cloud provider, offering agentless memory scanning to identify threats such as cryptomining malware within your virtual machines on Google Cloud.
The scalability of cloud technology has the potential to revolutionize security practices for businesses operating in today's threat landscape. With the increasing adoption of cloud technologies, built-in security solutions on cloud platforms are crucial in addressing emerging threats for organizations. For instance, the recent Google Cybersecurity Action Team Threat Horizons Report revealed that 86% of compromised cloud instances were exploited for cryptocurrency mining. VMTD is one of the measures we employ to safeguard our Google Cloud Platform customers against evolving attacks like coin mining, data exfiltration, and ransomware.
Google's innovative strategy with agentless VM threat detection
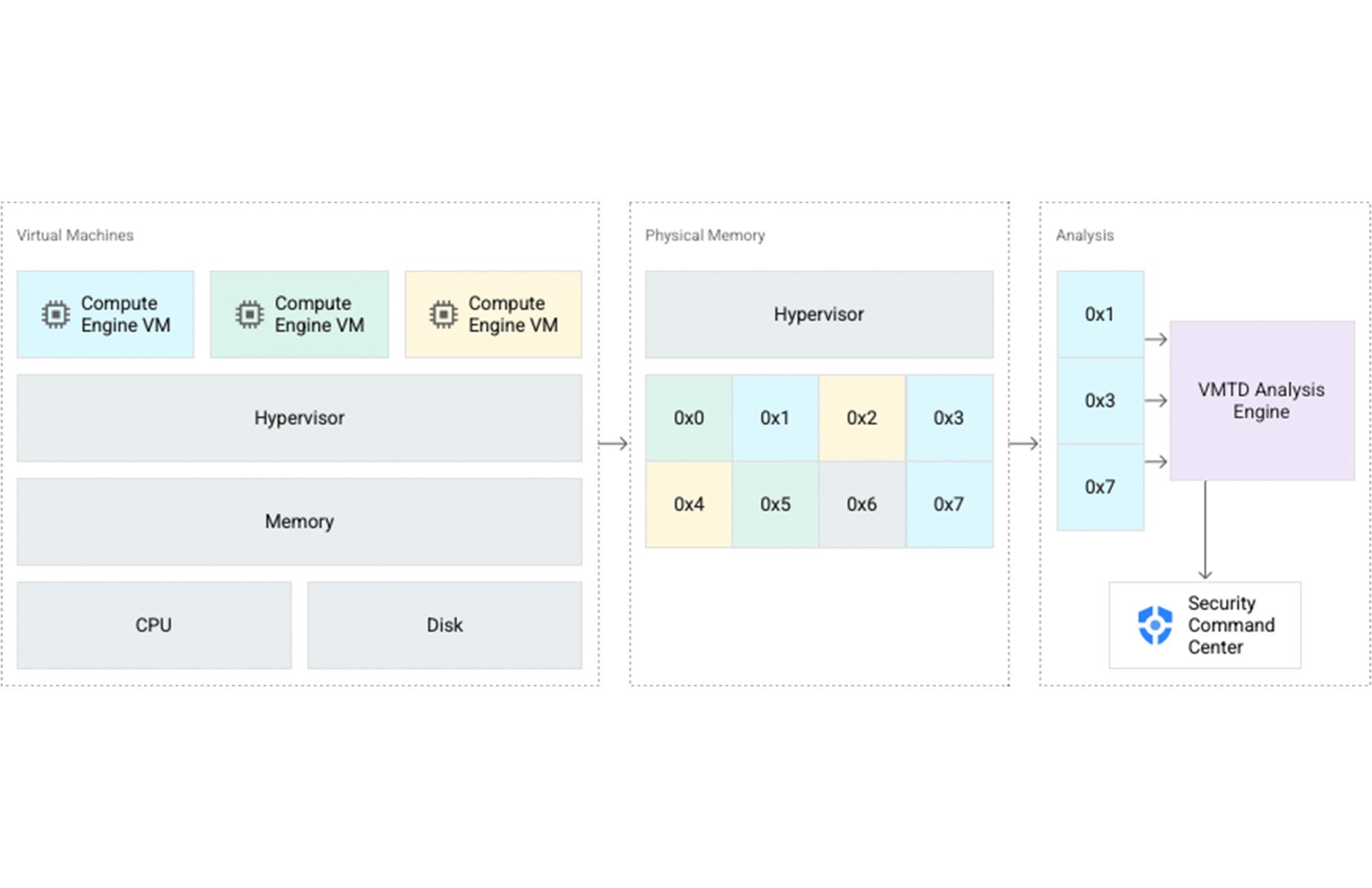
In the realm of traditional endpoint security, the common practice involves deploying software agents within guest virtual machines to gather signals and telemetry for real-time threat detection. However, cloud technology presents an opportunity to reimagine these existing models. With Compute Engine, our goal was to explore the possibility of collecting signals to aid in threat detection without requiring customers to run additional software. By avoiding the need for an agent inside their instance, we minimize the impact on performance, reduce the operational burden of agent deployment and management, and decrease the attack surface for potential adversaries.
Through our exploration, Google discovered that we could leverage the hypervisor—the software that operates underneath and orchestrates our customers' virtual machines—to incorporate highly effective and tamper-resistant threat detection capabilities.
Getting Started with Virtual Machine Threat Detection (VMTD)
Discover the incredible potential of VMTD and its ability to detect cryptomining attacks. To begin utilizing VMTD, simply navigate to the Settings page in Security Command Center and select "MANAGE SETTINGS" under Virtual Machine Threat Detection. From there, you can customize the scope of VMTD to suit your needs. To verify its effectiveness in your environment, try downloading and executing this test binary that emulates cryptomining activity.
Ensuring Customer Confidence
Ensuring the trust of our users in Google Cloud is of utmost importance to us. We are committed to taking various measures to guarantee that VMTD thoroughly examines workloads for potential threats while maintaining and preserving trust.
-
First, VMTD is available as an opt-in service for our Security Command Center Premium customers.
-
Additionally, not only does Confidential Computing provide encryption for memory as it moves out of a CPU to RAM, we never process memory in VMTD from Confidential nodes.
Advanced threat detection with SCC Premium
VMTD seamlessly integrates with Security Command Center Premium, offering a comprehensive defense system. Combined with the powerful threat detection capabilities of Event Threat Detection and Container Threat Detection, these three layers provide holistic and robust protection for workloads operating on Google Cloud.

In addition to its robust threat detection capabilities, the premium version of Security Command Center serves as a comprehensive security and risk management platform exclusively designed for Google Cloud. It offers a wide range of built-in services that empower you to gain full visibility into your cloud assets, effortlessly identify misconfigurations and vulnerabilities in your resources, and seamlessly maintain compliance with industry standards and benchmarks.
To unlock the full potential of Security Command Center's premium features, simply reach out to our dedicated Google Cloud team for a free consultation. Contact our team
For more in-depth information about all these exciting new capabilities in SCC, we encourage you to explore the video Walkthrough










 Twitter
Twitter Youtube
Youtube